If you get “access denied” or “Insufficient rights” errors, then you may have bumped up against some built-in protections that are provided by the AdminSDholder AD DS function set. Simply, every 20 minutes or so, this process goes through and resets rights and permissions on certain accounts in AD. This will screw up Exchange and Lync migrations because users in specific groups stop inheriting perms from above (they are protected!). Going in an twiddling one check box fixes the situation, but you need to know where and why.
After reading this excellent blog article by AD DS MVP John Policelli, try this.
Uh oh. that blog article cannot be found no more! Try this location instead:
https://technet.microsoft.com/en-us/magazine/2009.09.sdadminholder.aspx
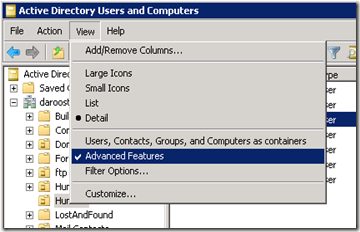
First, make sure your ADUC is set to show advanced features:
Then, take a look at the account that is giving you the error:
locate the user object, select properties | security | advanced, and then tick the check box indicated by balloon #3.

I think that I have seen this issue at least once (literally) in every Lync, OCS, and Exchange project I have worked on in the last 10 years. The best practice, of course, would never have one of those protected group members with an email account or Lync/OCS account, but we know that is not always practical or enforced.
YMMV.


No comments:
Post a Comment